Secure Research
The Cybersecurity Maturity Model Certification, (CMMC) was created by the Department of War (DoW) to better safeguard Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). The CMMC applies to anyone participating in Federal research at the University of Oregon, and is used to ensure that researchers have acceptable safeguards in place to protect sensitive information.
Researcher Responsibilities
Researchers handling Federal Contract Information (FCI) at the University of Oregon must meet the basic safeguards defined under CMMC Level 1. These safeguards include implementing 15 fundamental cybersecurity practices—such as limiting system access, securing physical devices, and protecting information during transmission—to ensure FCI is not improperly accessed or disclosed. To remain compliant, researchers must ensure that any systems processing or storing FCI follow these controls, complete an annual self‑assessment, and submit results and affirmations to the DoW’s Supplier Performance Risk System (SPRS).
Definitions
- Federal Contract Information (FCI): As defined in section 4.1901 of the Federal Acquisition Regulation (FAR), FCI is “information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, excluding information provided by the Government to the public (such as that on public websites) or simple transactional information, such as that necessary to process payments.”
- Controlled Unclassified Information (CUI): As outlined in Title 32 CFR 2002.4(h), CUI is “information the Government creates or possesses, or that an entity creates or possesses for or on behalf of the Government, that a law, regulation, or Government-wide policy requires or permits an agency to handle using safeguarding or dissemination controls.” For more information regarding specific CUI categories and subcategories, see the DoW CUI Registry website.
Mission Plan
CMMC program requirements will apply to all DoW solicitations and contracts for which a defense contractor or subcontractor will process, store, or transmit FCI or CUI on its unclassified contractor information systems. This includes new DoW solicitations, New DoW procurement instruments including contracts, task orders, delivery orders, and their associated option periods, as a condition to exercise and option period, and subcontractors subject to flow-down requirements.
- Phase 1: Begins on November 10, 2025. Where applicable, solicitations will require level 1 or 2 self-assessments
- Phase 2: Begins on November 10, 2026. Where applicable, solicitations will require level 2 certification
- Phase 3: Begins on November 10, 2027. Where applicable, solicitations will require level 3 certification
- Phase 4: Begins on November 10, 2028. All solicitations and contracts will include applicable CMMC level requirements as a condition of contract award.
The CMMC Diagram is split into three categories of compliance. Please regard the table as for what kind of security measures are required in your research. The certification levels align with the type and sensitivity of information that must be protected.
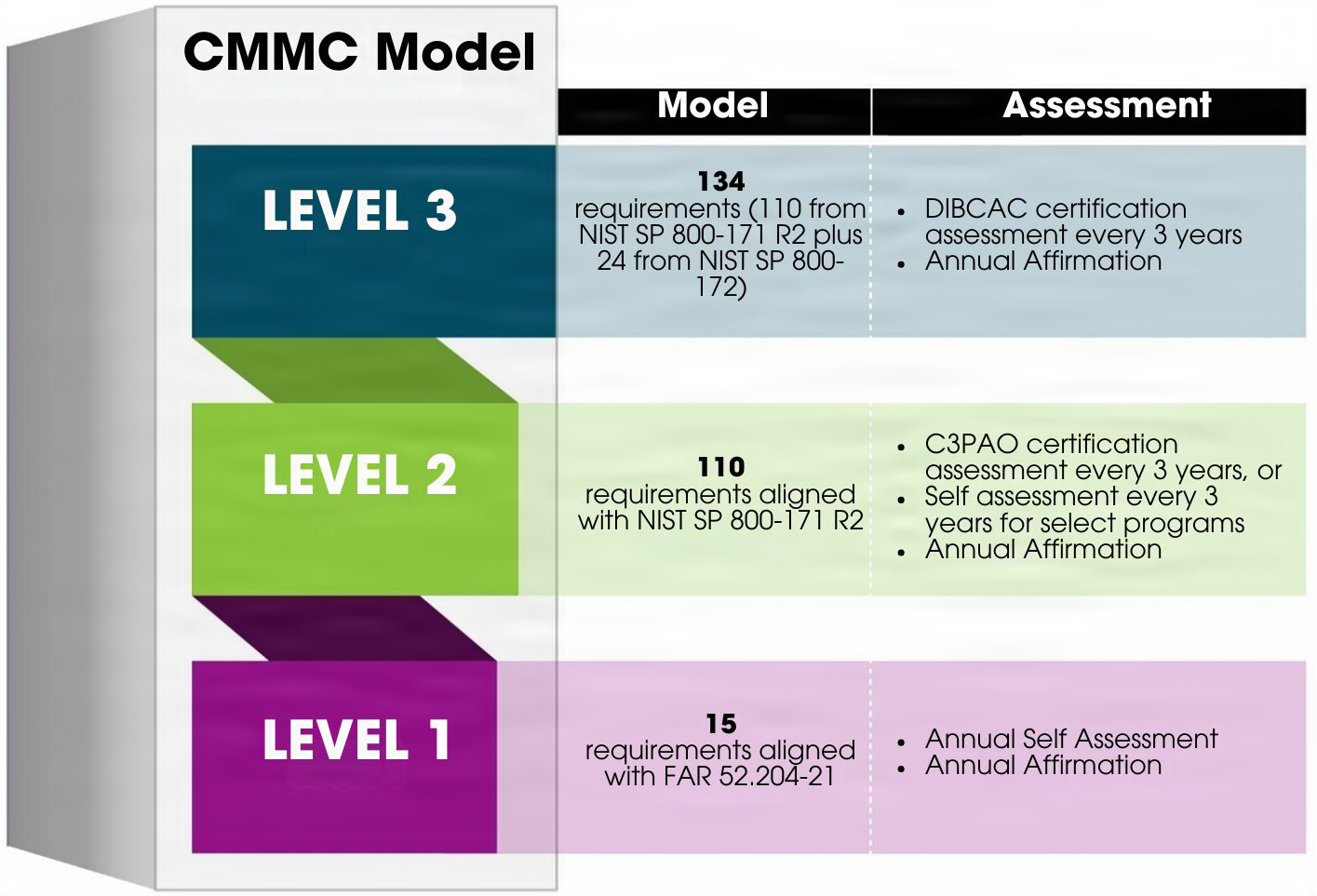
| CMMC Level | Information Protected | Security Requirement Source | Assessment Type(s) | Assessment Frequency |
|---|---|---|---|---|
| Level 1 | Federal Contract Information (FCI) | 15 basic safeguarding practices from FAR clause 52.204-21 | Annual Self-Assessment entered into the Supplier Performance Risk System (SPRS) | Annually |
| Level 2 | Controlled Unclassified Information (CUI) | 110 requirements aligned with NIST 800-171 Revision 2 (R2) required by DFARS clause 252.204-7012 | Self-Assessment or Certified Third-Party Assessor Organization (C3PAO) entered into SPRS | Triennially (Every 3 years) |
| Level 3 | CUI with Enhanced Protection | 110 requirements from NIST 800-171 Revision 2 (R2) required by DFARS clause 252.204-7012 plus 24 selected requirements from NIST 800-172 Feb 2021 | Government assessment by Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) entered into SPRS | Triennially (Every 3 years) |
Details by CMMC level
- Level 1 (Self): Focuses on the basic safeguarding requirements necessary to protect FCI. Organizations Seeking Assessment (OSAs) must successfully implement all 15 requirements. No Plans of Action and Milestones (POA&Ms) are permitted.
- Level 2 (Self or C3PAO): Focuses on the comprehensive protection of CUI. For contracts requiring this level, the assessment type depends on the criticality and sensitivity of the information. Some organizations may satisfy the requirement with an OSA-conducted self-assessment. For contracts requiring higher assurance, the Organization Seeking Certification (OSC) must hire an authorized or accredited CMMC third-party assessment organization or C3PAO to conduct the assessment.
- Level 3 (DIBCAC): Focuses on providing enhanced protection against Advanced Persistent Threats (APTs). This assessment is conducted by the government’s DCMA Defense Industrial Base Cybersecurity Assessment Center (DIBCAC). A prerequisite for initiating this assessment is achieving a CMMC Status of Final Level 2 (C3PAO) for the systems in scope.
Learn More
- CMMC Website: Official CMMC Website Link
- About CMMC: CMMC Website About Page
- NIST 800-171 R2: NIST 800-171 Revision 2: Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations
- FAR 52.204-1: Basic Safeguarding of Covered Contractor Information Systems
- Relevant DFARS Clauses
- DFARS Clause 252.204-7012: Safeguarding Covered Defense Information and Cyber Incident Reporting
- DFARS Provision 252.204-7019: Notice of NIST 800-171 DoD Assessment Requirements
- DFARS Clause 252.204-7020: NIST SP 800-171 DoD Assessment Requirements
- DFARS Clause 252.204-7021: Cybersecurity Maturity Model Certification Requirements
Research Support
If you have any questions regarding how your research data should be treated at the University of Oregon, please contact the Information Security Office at infosec@uoregon.edu.
